Smishing is an attack that is still too current and always proves to be very effective. What is it, and what does it have to do with the SMS spoofing technique? Because cybercriminals are using these tools. The use of SMS by users is now marginal: historical text messages are a communication tool long since replaced by instant messaging clients and more advanced implementations such as the RCS protocol.
However, SMS continues to remain an essential means for companies, which are thus sure of being able to reach customers regardless of the type of mobile device used (SMS are managed with a simple feature phone without the functionality of smartphones) and without the need for the presence of a particular app. At the same time, unfortunately, phenomena such as smishing and SMS spoofing are continually growing; these are levers on which cybercriminals are increasingly acting to steal credentials and personal data.
What Is Smishing?
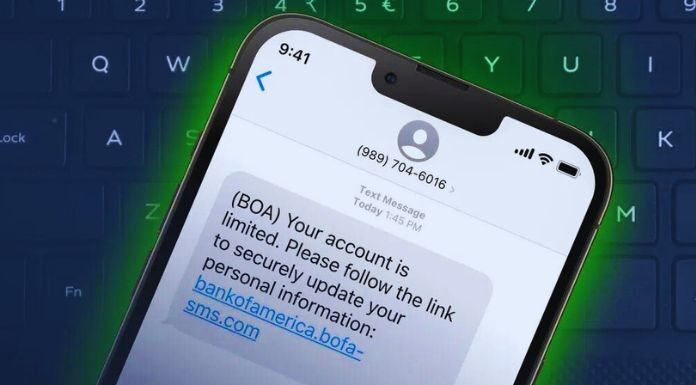
Smishing, an abbreviated form of SMS phishing, is an attack used by attackers to trick the user into visiting a malicious site, downloading malware, or executing a dangerous file by following the link contained in the text message. The goal of smishing attacks is to steal not only passwords and login credentials but also other personal data such as credit card numbers, email addresses, social security numbers, residential addresses, and so on.
In the case of the most advanced computer scams, attackers use reverse proxies that act as intermediaries between the user’s device and the actual servers of a bank, an online service, or an operator. As done with EvilProxy, therefore, attackers can also bypass two-factor or even multi factor authentication (MFA) mechanisms.
SMS Spoofing: What Is It?
The SMS spoofing system permits aggressors to change the shipper of the message to fool the client into accepting that the correspondence comes from a confided-in touch or is sent by a famous organization dynamic on a public or global scale. For instance, a gathering of tricksters can change the name of the source of the SMS to cause the beneficiary to accept that the message comes from a bank, a broadcast communications administrator, or a specialist co-op of any sort.
Consider the model picture distributed below: for this situation, the principal SMS shows an OTP (once secret key ) code from Post for verification on policy management administrations with SPID. The SMS reports use PosteInfo as the shipper and are totally genuine and supportive of getting to numerous web-based administrations. The last SMS, nonetheless, is an instance of smishing that utilizes the SMS caricaturing strategy to change the natural source of the message.
As may be obvious, the aggressor has set PosteInfo as the source and attempts to send the casualty to a site intended to urge him to enter his qualifications. In this situation, the message of the SMS could be better, and the connection embedded in the message could be more solid. At any point, could Poste Italiane utilize a URL-shortening administration like bit.ly? In no way, shape or form. Or, it wouldn’t request that you affirm your login certifications; no credit foundation does this.
A somewhat hurried client, deceived by a superior imagined false message, could, notwithstanding, fall into the snare of seeing an SMS show up, which evidently appears to be genuine under different explanations from a similar bank or organization beforehand. The figure shows an attempt at smishing that involves a similar plan as the past one; the main distinction is that for this situation, the screen was taken from an Android gadget, while in the figure distributed simply above, it was taken from an iOS gadget.
How The SMS Spoofing Technique Works
As we have seen, the SMS mocking method comprises sending SMS so that they seem to have been sent by someone else. This is finished by changing the shipper’s name, telephone number, or both. The truth of the matter is that the activity isn’t in any way, shape, or form hard to perform. In BackTrack and some versions of the Kali Linux distribution, there is a tool called Social Engineering Toolkit (SET), which allows you to send SMS to third parties by altering the number and name of the sender.
There are even companies that offer SMS spoofing services that can be purchased online. Anyone with a minimum amount of computer knowledge can, therefore, send messages by pretending to be someone else. How can these uses be legitimate? And how can there be companies that sell the possibility of accessing SMS spoofing mechanisms? In some cases, senders of SMS sent on a large scale to their customers do not wish to display telephone numbers but only a string that allows them to be identified on the recipients’ terminals.
It can happen when you have to send “service” messages to which the recipient user must not be able to respond. This is why techniques are used to set the sender of the SMS and hide the telephone number used. Some examples of smishing are automatically filtered by the protection system integrated into the SMS management app. The image shows an example of an automatic block by Google Messages. However, it is best not to trust these protection solutions unquestioningly; some smishing messages with a spoofed SMS sender still escape control.
Therefore, pay attention to all communications you receive, never enter personal data and authentication credentials in the web pages reported in an SMS, and refrain from visiting addresses hidden behind abbreviated addresses or referring to domains other than the official ones belonging to the company. In this regard, it is worth focusing on what a URL is and its structure; understanding which addresses are not managed by a company or organization by analyzing the domain name is essential.
Also Read: Embedded Software: Understand Its Corporate Utility